The highly secretive Five Eyes alliance has disrupted a China-backed hacker group – in an unusually public manner
- Written by: Dennis B. Desmond, Lecturer, Cyberintelligence and Cybercrime Investigations, University of the Sunshine Coast
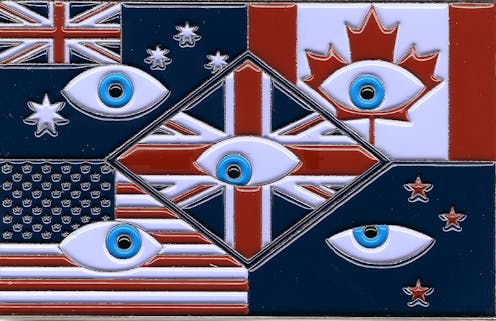
This week the Five Eyes alliance – an intelligence alliance between Australia, the United Kingdom, Canada, New Zealand and the United States – announced its investigation[1] into a China-backed threat targeting US infrastructure.
Using stealth techniques, the attacker – referred to as “Volt Typhoon” – exploited existing resources in compromised networks in a technique called “living off the land[2]”.
Microsoft made a concurrent announcement[3], stating the attackers’ targeting of Guam was telling of China’s plans to potentially disrupt critical communications infrastructure between the US and Asia region in the future.
This comes hot on the heels of news[4] in April of a North Korean supply chain attack on Asia-Pacific telecommunications provider 3CX. In this case, hackers gained access to an employee’s computer using a compromised desktop app for Windows and a compromised signed software installation package.
The Volt Typhoon announcement has led to a rare admission by the US National Security Agency that Australia and other Five Eyes partners are engaged in a targeted search and detection scheme to uncover China’s clandestine cyber operations.
Such public admissions from the Five Eyes alliance are few and far between. Behind the curtain, however, this network is persistently engaged in trying to take down foreign adversaries. And it’s no easy feat.
Let’s take a look at the events leading up to Volt Typhoon – and more broadly at how this secretive transnational alliance operates.
Uncovering Volt Typhoon
Volt Typhoon is an “advanced persistent threat group” that has been active since at least mid-2021. It’s believed to be sponsored by the Chinese government and is targeting critical infrastructure organisations in the US.
The group has focused much of its efforts on Guam. Located in the Western Pacific, this US island territory is home to a significant and growing US military presence, including the air force, a contingent of the marines, and the US navy’s nuclear-capable submarines.
It’s likely the Volt Typhoon attackers intended to gain access to networks connected to US critical infrastructure to disrupt communications, command and control systems, and maintain a persistent presence on the networks. The latter tactic would allow China to influence operations during a potential conflict in the South China Sea.
Australia wasn’t directly impacted by Volt Typhoon, according to official statements. Nevertheless, it would be a primary target for similar operations in the event of conflict.
As for how Volt Typhoon was caught, this hasn’t been disclosed. But Microsoft documents highlight previous observations of the threat actor attempting to dump credentials and stolen data from the victim organisation. It’s likely this led to the discovery of compromised networks and devices.
Living-off-the-land
The hackers initially gained access to networks through internet-facing Fortinet FortiGuard devices, such as routers. Once inside, they employed a technique called “living-off-the-land”.
This is when attackers rely on using the resources already contained within the exploited system, rather than bringing in external tools. For example, they will typically use applications such as PowerShell (a Microsoft management program) and Windows Management Instrumentation to access[5] data and network functions.
By using internal resources, attackers can bypass safeguards that alert organisations to unauthorised access to their networks. Since no malicious software is used, they appear as a legitimate user. As such, living-off-the-land allows for lateral movement within the network, and provides opportunity for a persistent, long-term attack.
The simultaneous announcements from the Five Eyes partners points to the seriousness of the Volt Typhoon compromise. It will likely serve as a warning to other nations in the Asia-Pacific region.
Who are the Five Eyes?
Formed in 1955[6], the Five Eyes alliance is an intelligence-sharing partnership comprising Australia, Canada, New Zealand, the UK and the US.
The alliance was formed after World War II to counter the potential influence of the Soviet Union. It has a specific focus on signals intelligence. This involves intercepting and analysing signals such as radio, satellite and internet communications.
The members share information and access to their respective signals intelligence agencies, and collaborate to collect and analyse vast amounts of global communications data. A Five Eyes operation might also include intelligence provided by non-member nations and the private sector.
Recently, the member countries expressed concern about China’s de facto military control over the South China Sea[7], its suppression of democracy in Hong Kong[8], and threatening moves towards Taiwan. The latest public announcement of China’s cyber operations no doubt serves as a warning that Western nations are paying strict attention to their critical infrastructure – and can respond to China’s digital aggression.
In 2019, Australia was targeted[9] by Chinese state-backed threat actors gaining unauthorised access to Parliament House’s computer network. Indeed, there is evidence that China is engaged in a concerted effort to target[10] Australia’s public and private networks.
The Five Eyes alliance may well be one of the only deterrents we have against long-term, persistent attacks against our critical infrastructure.
Read more: Deterring China isn't all about submarines. Australia's 'cyber offence' might be its most potent weapon[11]
References
- ^ announced its investigation (media.defense.gov)
- ^ living off the land (www.nsa.gov)
- ^ announcement (www.microsoft.com)
- ^ of news (www.nknews.org)
- ^ to access (www.microsoft.com)
- ^ Formed in 1955 (www.theguardian.com)
- ^ over the South China Sea (theconversation.com)
- ^ democracy in Hong Kong (theconversation.com)
- ^ targeted (theconversation.com)
- ^ effort to target (theconversation.com)
- ^ Deterring China isn't all about submarines. Australia's 'cyber offence' might be its most potent weapon (theconversation.com)

























